Proofpoint Isolation helps stop phishing attacks without the productivity-crimping effects of broad website blocks and similar controls. It gives IT and security teams an adaptive, risk-based control and added layer of security.
BENEFITS & FEATURES
Browsing sessions triggered from potentially risky URLs are automatically isolated from the corporate environment and made safe for users. Proofpoint Isolation protects University of Nebraska end-users from web-based malware attacks, URL-based phishing campaigns, and unknown or uncategorized domains.
If you open a potentially risky URL you received via email Proofpoint Isolation will open the landing page in a secure browser container. You will be able to view the contents of the site as normal, but uploading/downloading content is restricted while Proofpoint analyzes the website. Once Proofpoint Isolation has determined that the site is safe, you will be given the option to leave the isolated environment and load the full version of the website.
GETTING STARTED
Proofpoint Isolation does not require any download/install. If you are a member of a team that has been identified as at higher risk cyber attack your account will be configured with Isolation protection.
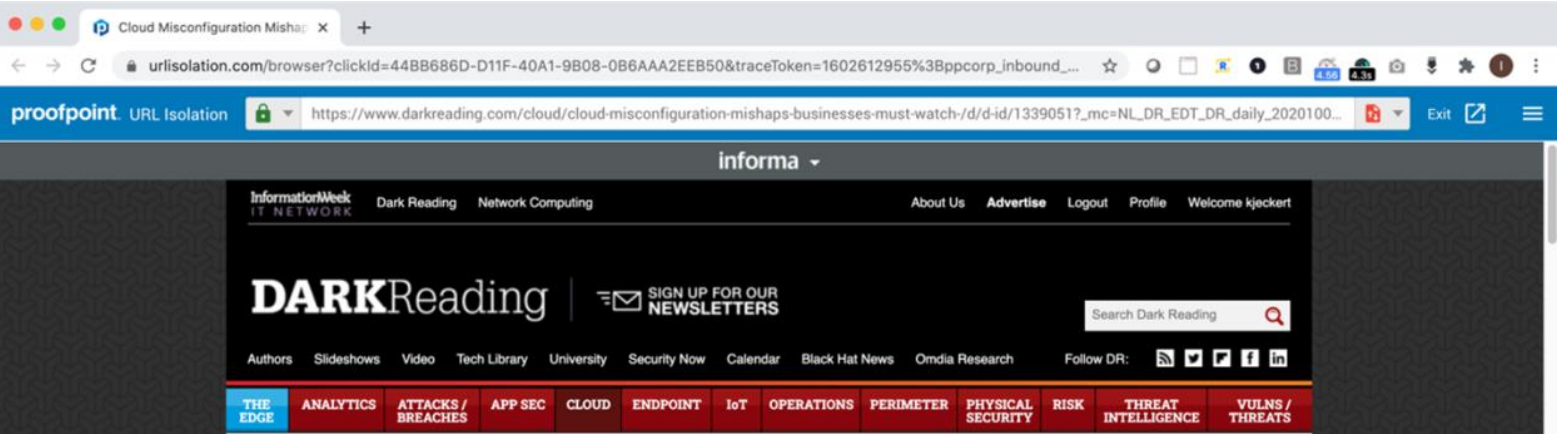
If you click a rewritten TAP URL in your email, it may redirect to the URL Isolation browser. The URL Isolation browsing session would appear like this:
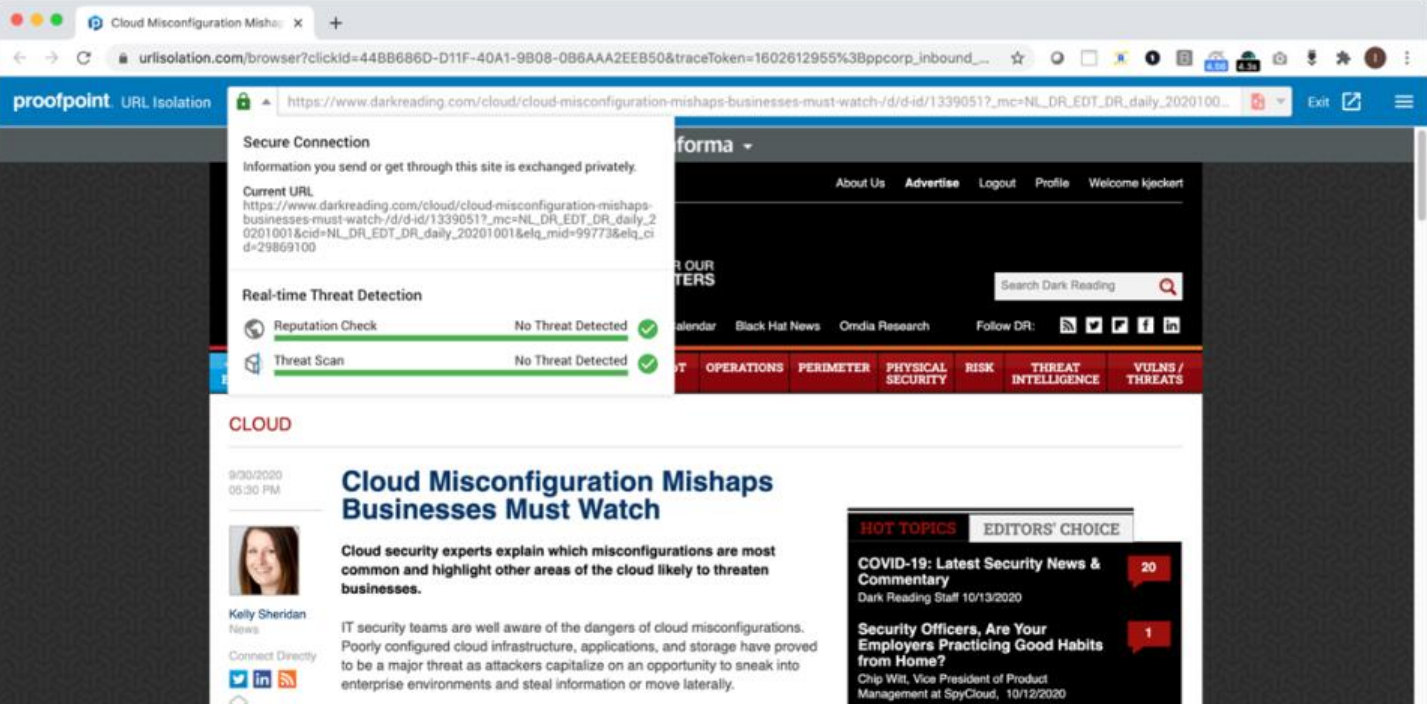
Click the icon to the left of the Isolated URL address to see progress bars for scanning of the page you are visiting:
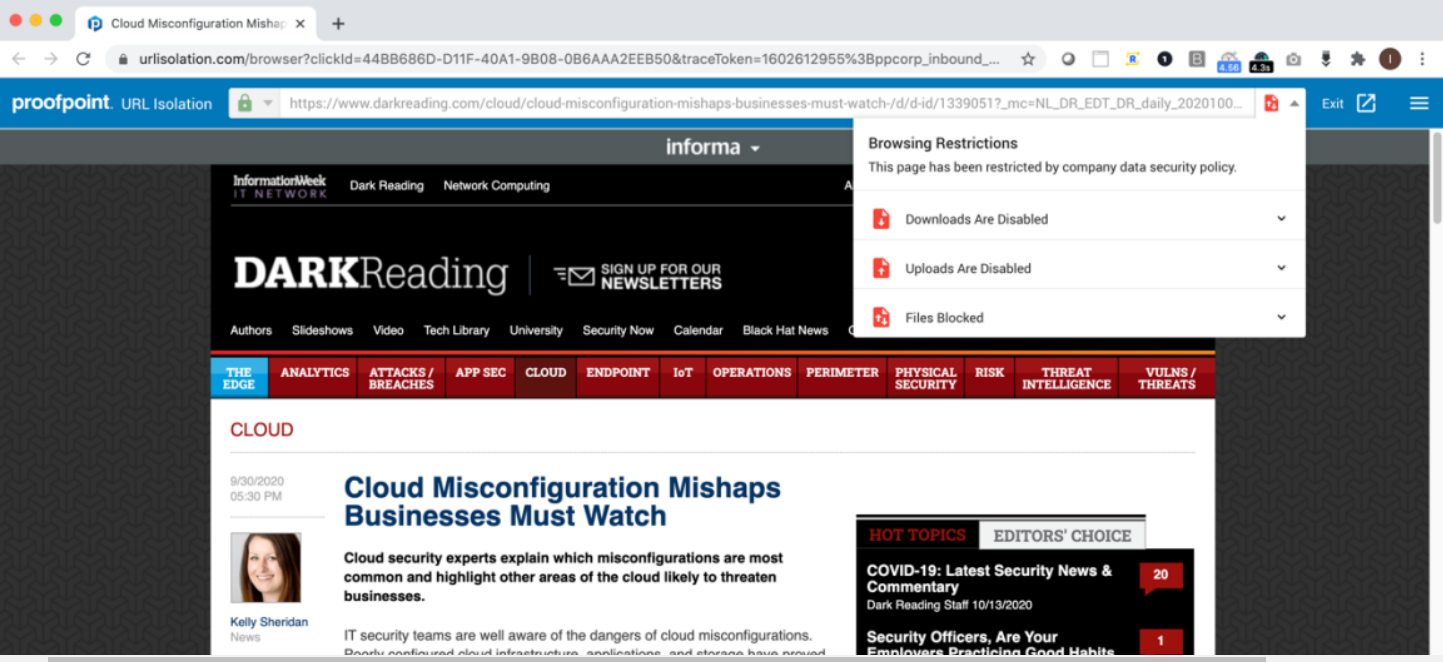
Uploads and downloads are disabled in Isolation. Additional browser restrictions are shown in the drop-down menu to the right of the URL bar.
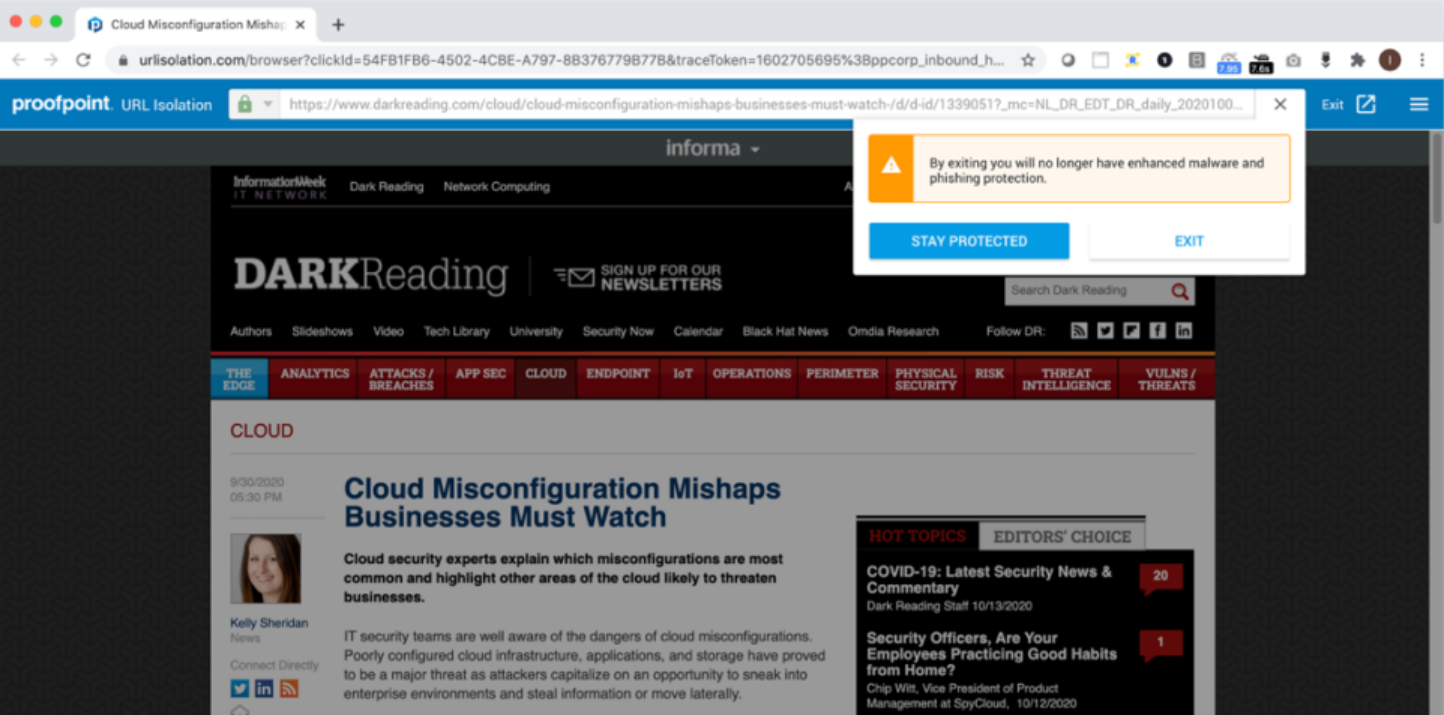
If scans determine there is no threat, an "Exit" button is provided on the right of the browser bar. Clicking “Exit” will display a warning, letting you know that leaving Isolation means you will no longer be protected from phishing or malware. Click “Stay Protected” to remain in Isolation, or “Exit” to open the site on your native browser.
If Proofpoint Isolation prevents access to a site or download that you believe has been mistakenly classified as "malicious" please contact its-sec-ops@nebraska.edu for assistance.